A significant security incident has impacted the official website of CPUID, a well-known provider of system information and monitoring utilities. For a period of less than twenty-four hours, unknown attackers compromised the domain cpuid[.]com to distribute trojanized versions of popular software.
The tools affected include CPU-Z, HWMonitor, HWMonitor Pro, and PerfMonitor. These applications are widely used by technology professionals, enthusiasts, and everyday users to check hardware specifications and monitor system temperatures and voltages.
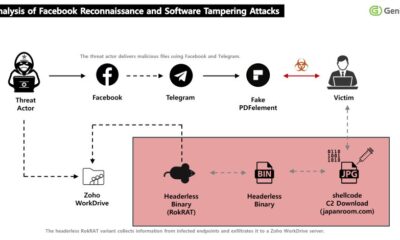
During the compromise, visitors who downloaded these tools from the official source received malicious executable files instead of the legitimate software. The incident represents a classic software supply chain attack, where a trusted distribution point is subverted to spread malware.
Timeline and Discovery of the Attack
The malicious activity occurred within a specific window. According to available reports, the website was compromised beginning around 15:00 UTC on April 9.
The threat actors maintained control until approximately 10:00 UTC on April 10. This brief but critical period was sufficient to infect an unknown number of users who visited the site for downloads.
Security researchers identified the campaign after detecting anomalous network traffic and file signatures associated with the downloads. The swift discovery likely limited the overall impact of the breach.
The STX RAT Payload
The primary payload delivered through the compromised installers was identified as STX RAT. RAT stands for Remote Access Trojan, a category of malware that provides attackers with extensive control over an infected system.
Once installed, a RAT can allow unauthorized actors to steal files, log keystrokes, activate webcams, and use the computer as part of a botnet. The STX variant is a known threat that has been used in various cyber-espionage and data theft campaigns.
The deployment method, hiding malware within seemingly legitimate hardware tools, is particularly effective. Users often run such software with elevated administrative privileges, granting the malware deeper access to the operating system.
Implications for Software Trust and Verification
This breach underscores a persistent vulnerability in the digital ecosystem: the integrity of software download portals. Even established and reputable websites can become targets and temporary vectors for attack.
It highlights the importance of secondary verification measures for users. These include checking file hashes provided by developers, using digital signature verification, and maintaining updated endpoint security software that can detect such compromises.
For software developers and website operators, the incident serves as a stark reminder of the need for robust web application security, continuous monitoring for unauthorized changes, and rapid incident response protocols.
The domain name itself, as the primary address for these trusted tools, became the initial point of failure. Ensuring the security of the domain registration and associated hosting infrastructure is a foundational step in preventing such events.
Response and Mitigation
Following the discovery of the breach, CPUID appears to have regained control of its website. The legitimate, clean versions of the affected software have been restored for download.
Users who downloaded CPU-Z, HWMonitor, or related tools from the official website during the 19-hour compromise window are strongly advised to run comprehensive antivirus scans. They should also consider downloading a fresh, clean copy from the now-secure site.
Security teams are analyzing the incident to determine the initial attack vector, whether through compromised credentials, a web application vulnerability, or a separate supply chain attack. This forensic analysis is crucial for preventing future occurrences.
The relatively short duration of the compromise suggests the attackers’ actions may have triggered internal alerts or that external security researchers provided prompt notification.
Looking forward, the security community expects CPUID to release a formal statement detailing the breach’s cause and the steps taken to prevent a recurrence. Independent security firms will likely publish deeper technical analyses of the STX RAT samples distributed in this campaign. Users and companies must remain vigilant, as threat actors continually refine their techniques to exploit trusted software sources and domain names.