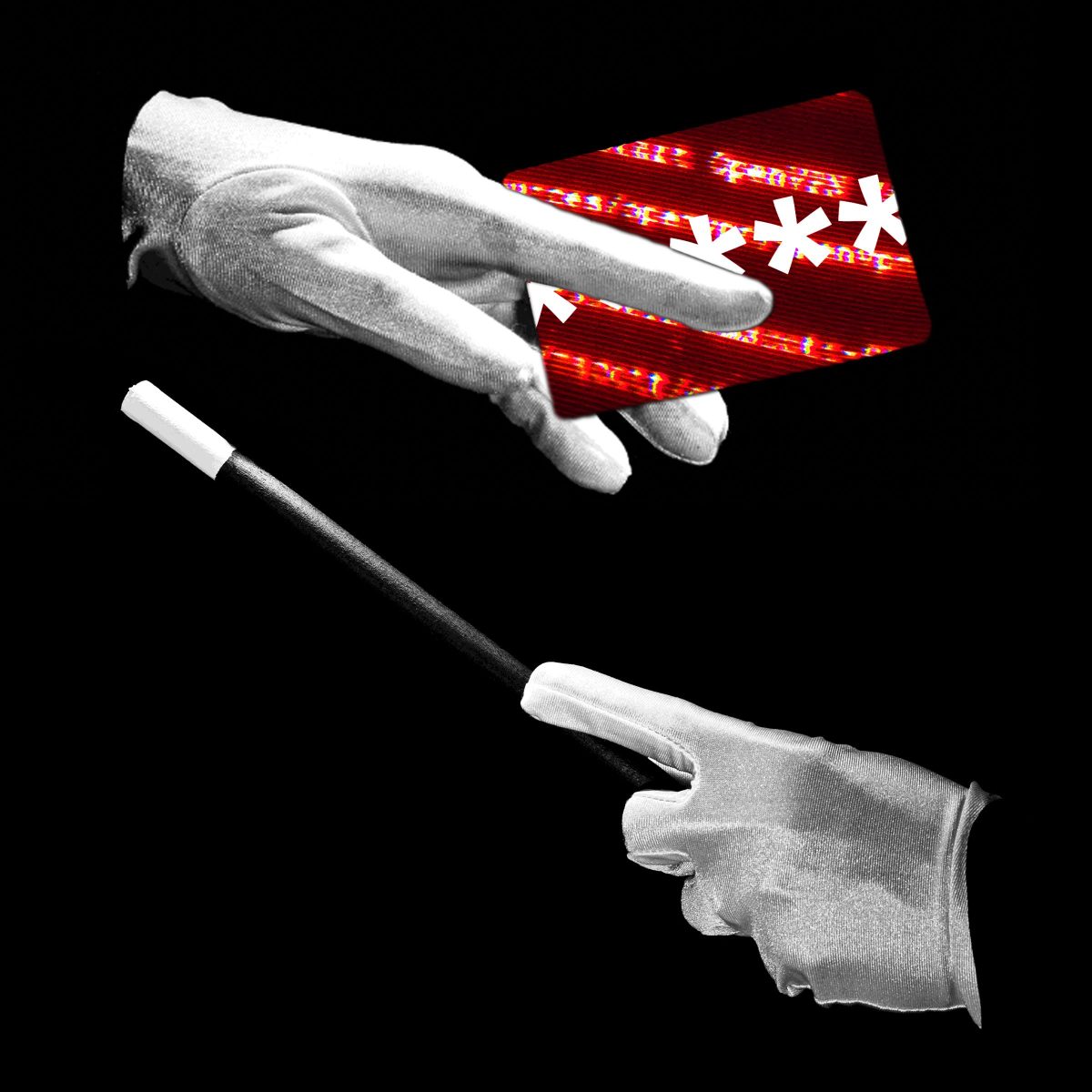
In a concerning development for the technology and cybersecurity sectors, a recent leak of proprietary code from the artificial intelligence company Anthropic is being weaponized by malicious actors. The stolen source code for the Claude AI assistant is reportedly being bundled with malware and distributed across various online platforms, posing a significant risk to unsuspecting developers and organizations.
This incident highlights a growing trend where valuable intellectual property, once exfiltrated, is used as bait in broader cyberattacks. Security researchers have observed that files purporting to contain the leaked Claude code are laced with trojans, backdoors, and other malicious payloads. Individuals downloading these files in the hope of accessing the AI code are instead compromising their own systems.
Broader Cybersecurity Landscape
The Claude code leak and its malicious repurposing occur against a backdrop of several high-profile security breaches. In a separate but related matter, the Federal Bureau of Investigation has assessed that a recent compromise of its wiretapping tools presents a national security risk. The breach of these sensitive surveillance systems could potentially undermine ongoing investigations.
Furthermore, the technology giant Cisco has confirmed that attackers successfully stole portions of its source code. This theft is believed to be part of a persistent and sophisticated supply chain hacking campaign targeting critical infrastructure providers. Such attacks aim to infiltrate widely used software and hardware at its source, creating vulnerabilities that can be exploited downstream across countless customer networks.
Implications for Digital Trust and Security
The convergence of these events underscores the multifaceted nature of modern cyber threats. The weaponization of a code leak demonstrates how data breaches can have secondary, cascading effects far beyond the initial theft. For businesses operating online, these incidents reinforce the critical importance of robust cybersecurity hygiene.
Organizations are advised to treat unsolicited software or code repositories with extreme caution, especially those circulated on unofficial channels. The promise of exclusive access to leaked proprietary technology is a common social engineering tactic. Security teams should also remain vigilant for indicators of compromise linked to these specific malware campaigns.
These breaches also raise complex questions about the security of foundational digital tools and the integrity of the software supply chain. When source code from major vendors like Cisco is compromised, the potential for widespread systemic risk increases dramatically. It necessitates a renewed focus on securing development environments and implementing stringent access controls.
Looking ahead, cybersecurity firms and law enforcement agencies are actively tracking the distribution of the malware-laden Claude code packages. The investigation into the original leak and the subsequent malicious activity is ongoing. Anthropic and affected companies like Cisco are likely conducting internal forensic audits to determine the full scope of the breaches and to harden their defenses against future intrusions.
In the coming weeks, the industry can expect further advisories from cybersecurity authorities detailing technical indicators and mitigation strategies. The resolution of these incidents will depend on coordinated efforts between private sector security researchers and government agencies to identify the perpetrators and dismantle the infrastructure supporting these attacks.