A significant security vulnerability has been identified in Docker Engine, posing a substantial risk to containerized environments. The flaw, cataloged as CVE-2026-34040, carries a high CVSS score of 8.8. It allows a threat actor to circumvent authorization plugins, known as AuthZ plugins, under specific conditions. This bypass could potentially lead to unauthorized access to the underlying host system.
The vulnerability represents a continuation of a previously addressed security issue. It originates from an incomplete fix for CVE-2024-41110, a critical vulnerability in the same authorization component disclosed in July 2024. The persistence of this flaw highlights the challenges in comprehensively securing complex software subsystems.
Understanding the Authorization Bypass Mechanism
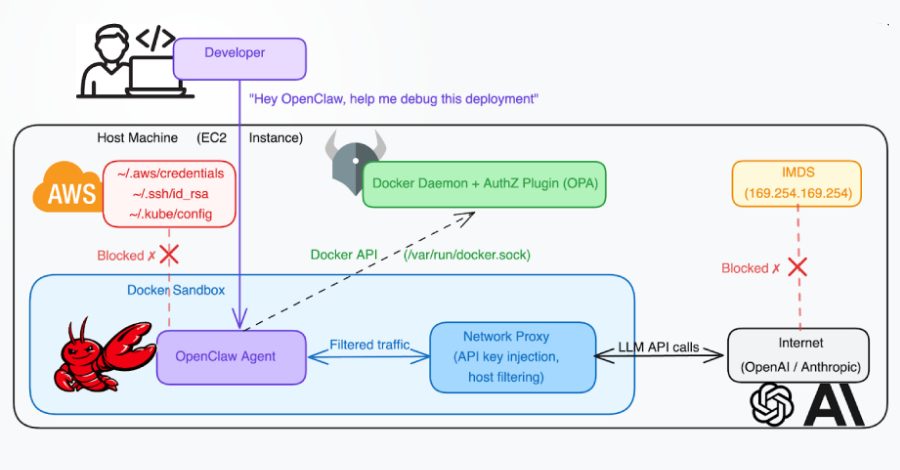
Docker’s authorization plugin framework is designed to provide granular control over user actions. It acts as a gatekeeper, intercepting API requests to determine if they should be permitted. The newly discovered weakness undermines this security layer.
By exploiting CVE-2026-34040, an authenticated user could execute commands that the AuthZ plugin would typically block. The specific circumstances required for exploitation are not fully detailed publicly to prevent immediate weaponization. However, the high severity score indicates a relatively low attack complexity with significant impact.
Implications for Container Security
This vulnerability has serious implications for organizations relying on Docker for container orchestration. A successful exploit compromises the fundamental principle of least privilege within the container environment. It erodes the security boundary between containers and the host operating system.
Gaining host access is a primary objective for attackers in containerized deployments. From the host, an adversary can potentially inspect data from all other containers, deploy persistent malware, or move laterally across a network. This makes CVE-2026-34040 a critical concern for production systems.
The flaw specifically affects deployments where custom or third-party AuthZ plugins are in use to enforce security policies. Environments relying solely on Docker’s default configuration without additional authorization plugins may not be vulnerable to this particular bypass method.
The Challenge of Patch Management
The fact that this flaw stems from an incomplete prior fix underscores a recurring theme in cybersecurity. Patching is often a complex process, and remediating one vector can sometimes inadvertently leave another path open. This incident serves as a case study in the need for thorough regression testing following security updates.
Organizations must maintain vigilant patch management strategies, especially for core infrastructure like container engines. The linkage between CVE-2024-41110 and CVE-2026-34040 demonstrates that a single fix may not fully resolve the underlying architectural weakness.
Recommended Mitigation and Response
The Docker maintainers have released an official security advisory addressing CVE-2026-34040. The primary mitigation is to promptly upgrade Docker Engine to the patched versions specified in the advisory. System administrators should prioritize this update, particularly for internet-facing or multi-tenant Docker deployments.
Until patches can be applied, organizations should review and potentially tighten network security controls around Docker daemons. Restricting access to the Docker API to only trusted, necessary users and systems can reduce the attack surface. Monitoring for unusual container creation or privilege escalation attempts is also advised.
Security teams should audit their Docker logs for any suspicious activity that may have occurred prior to patching. The vulnerability could have been exploited in a targeted manner before public disclosure. A comprehensive review of user and service accounts with Docker access is also a prudent step.
Broader Impact on the Container Ecosystem
This disclosure affects the wider container and cloud-native ecosystem. Many platforms and managed services build upon Docker Engine or maintain compatibility with its API. Providers of these services are likely assessing their own exposure and rolling out backend updates.
The vulnerability reinforces the importance of defense-in-depth strategies for container security. Relying on a single authorization mechanism is insufficient. Security practices such as regular image scanning, runtime threat detection, and strict network policies remain essential complementary controls.
Looking forward, the Docker security team and the open-source community are expected to conduct a deeper audit of the authorization plugin framework. The goal will be to identify and rectify any similar logic flaws to prevent future bypasses. Further clarifications on the exact preconditions for exploitation may also be forthcoming as the patch is disseminated and analyzed.
The resolution of CVE-2026-34040 is anticipated to be a focal point in the upcoming Docker Engine release notes. Independent security researchers will likely scrutinize the fix to ensure its completeness. This process contributes to the overall robustness of a tool fundamental to modern software deployment.