A significant new cybersecurity vulnerability has been identified in high performance graphics processing units, or GPUs. Academic researchers have documented a series of attacks that exploit a known hardware weakness called RowHammer, specifically targeting the GDDR6 memory commonly used in modern graphics cards. These attacks, collectively referred to in research as GPUBreach, GDDRHammer, and GeForge, represent a serious escalation in potential threats against systems leveraging these powerful processors.
The core of the vulnerability lies in the physical design of dynamic random access memory, or DRAM. RowHammer is a phenomenon where rapidly and repeatedly accessing, or hammering, a specific row of memory cells can cause electrical interference. This interference can induce bit flips in adjacent rows, inadvertently changing a 1 to a 0 or vice versa in memory locations the attacker should not have access to modify.
While RowHammer attacks against central processing unit, or CPU, memory have been known for nearly a decade, this new research demonstrates their viability against the graphics double data rate type six synchronous dynamic random access memory, or GDDR6 SDRAM, used in GPUs. The higher density and different architecture of this video memory were found to be susceptible to similar manipulation techniques.
From Bit Flips to System Control
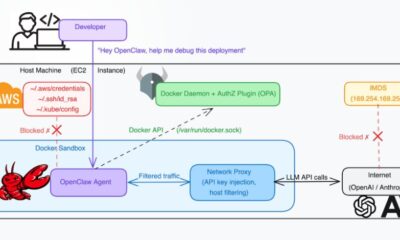
The GPUBreach attack methodology takes this fundamental flaw a critical step further. By carefully inducing these bit flips in GPU memory, an attacker with limited initial access to a system could potentially escalate their privileges. In the most severe scenarios documented, this could lead to gaining full control over the host computer.
This is possible because modern computing architectures increasingly treat the GPU not just as a graphics renderer but as a general purpose co processor. They handle a wide variety of computational tasks, from scientific simulations and artificial intelligence model training to video encoding. This integration means a compromise of the GPU’s security perimeter can have dire consequences for the entire system’s integrity.
The attack represents a cross component privilege escalation. It begins from a lower privilege environment on the GPU itself and, through the engineered memory errors, can breach the isolation between the GPU and the main system CPU. This bypasses critical security boundaries that operating systems and hypervisors rely upon to maintain system safety.
Implications for Cloud and Enterprise Security
The discovery has broad implications for data center and cloud security postures. Cloud service providers and enterprises frequently use servers equipped with high end GPUs for computationally intensive workloads. These environments often rely on strong isolation between different customers’ virtual machines or containers running on the same physical hardware.
A successful GPUBreach style attack could theoretically allow one tenant to break out of their isolated environment and access data or resources belonging to another tenant on the same server. This directly challenges the fundamental security model of public cloud infrastructure and high density computing.
Furthermore, the attack vector is particularly concerning because it exploits a hardware level flaw. While software vulnerabilities can often be patched with updates, mitigating a hardware based issue is far more complex. It typically requires changes to memory access patterns controlled by the GPU driver or, ultimately, a redesign of the memory chips themselves.
Security researchers note that exploiting this vulnerability requires local access to the machine, meaning it is not a remotely executable attack over a network in its basic form. However, it could be chained with other software vulnerabilities to create a more potent remote threat. It also highlights the growing attack surface presented by complex, heterogeneous computing systems where CPUs, GPUs, and other accelerators interact closely.
The research underscores an ongoing shift in cybersecurity focus. As computational workloads diversify across different processing units, attackers are following suit, probing for weaknesses in every component of the modern computing stack. The GPU, once considered a peripheral device, is now firmly in the spotlight as a critical security frontier.
Looking ahead, the research community and affected hardware vendors are expected to analyze these findings in detail. Mitigation strategies will likely be developed at both the software and firmware levels to monitor for and prevent the specific memory access patterns that enable RowHammer attacks on GDDR6. Long term, memory manufacturers may need to incorporate more robust RowHammer protection, known as Target Row Refresh, or TRR, into future generations of graphics memory. The disclosure timeline and the development of official patches will depend on coordinated efforts between academic researchers, GPU manufacturers, and major operating system developers.