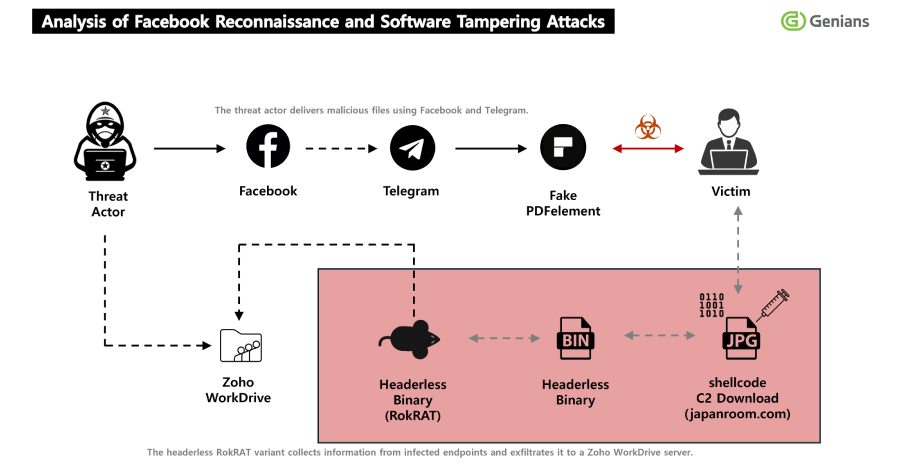
A sophisticated cyber espionage campaign attributed to North Korea has been uncovered, revealing a calculated exploitation of social media trust. The state-aligned hacking collective known as APT37, also tracked as ScarCruft, has been linked to a new multi-stage operation. This campaign leverages Facebook’s social environment as a primary vector for delivering a powerful remote access trojan called RokRAT.
The threat actors initiated contact by approaching potential targets on the social media platform. They strategically sent friend requests to individuals of interest, often those with connections to sectors like government, defense, or journalism. This initial step was designed to bypass traditional email security filters and establish a facade of legitimacy.
Once a connection was accepted, the operatives engaged in what appeared to be normal, benign conversation. This trust-building phase, sometimes lasting for weeks, was a critical component of the social engineering attack. The goal was to lower the target’s guard and create a perceived personal rapport.
After establishing trust, the attackers shifted tactics. They began sharing malicious files under the guise of ordinary documents, such as news articles, reports, or photographs. These files were typically delivered via Facebook Messenger or through links to compromised or attacker-controlled websites.
Technical Execution and Malware Payload
The delivered files were not the final payload but rather sophisticated downloaders. These initial files, often disguised as PDFs or documents, contained hidden code designed to fetch and execute the next stage of the attack from a remote server. This multi-stage approach makes detection by standard antivirus software more difficult.
The ultimate payload in this campaign is identified as RokRAT, a custom remote access trojan associated exclusively with APT37. RokRAT provides attackers with extensive control over a compromised system. Capabilities include file theft, screen capture, keylogging, and the execution of arbitrary commands. It is designed for persistent, long-term espionage.
The malware employs various techniques to evade detection and maintain its presence on infected machines. It can communicate with command and control servers using encrypted channels, often blending its traffic with legitimate web services to avoid raising network alarms.
Attribution and Historical Context
Attribution to APT37 is based on technical indicators, infrastructure overlaps, and the unique use of the RokRAT malware. This group is believed to operate on behalf of North Korean interests, focusing on intelligence gathering from targets primarily in South Korea, Japan, and other parts of Asia, though its campaigns have a global reach.
APT37’s activities have been documented for several years, with campaigns targeting think tanks, defectors, government employees, and media organizations. Their toolset is constantly evolving, but their reliance on social engineering as an initial access point remains a consistent and effective tactic.
This latest campaign underscores a shift towards leveraging major, trusted social media platforms as attack surfaces. It highlights how cyber adversaries are adapting their methods to exploit human psychology where purely technical defenses may fall short.
Implications for Digital Security
The incident serves as a stark reminder of the advanced persistent threat landscape. It demonstrates that even on platforms designed for social connection, malicious actors are conducting highly targeted reconnaissance and attacks. The line between social networking and cyber warfare continues to blur.
For organizations and individuals, the campaign reinforces the necessity of comprehensive security awareness training. Employees must be educated on the risks of accepting connection requests from unknown individuals, even on personal social media accounts, as these can be leveraged for professional targeting.
Technical defenses must also adapt. Security solutions need to monitor for anomalous behavior stemming from seemingly legitimate applications and scrutinize outbound communications that may be disguised as normal web traffic. The use of document analysis tools that can detect hidden macros or malicious code is also critical.
Based on the historical patterns of APT37, cybersecurity researchers expect this campaign to be ongoing and evolving. The group is likely to continue refining its social engineering lures and may shift to other platforms if Facebook’s security measures become more effective at disrupting their current methodology. Future iterations of RokRAT or similar malware with enhanced stealth capabilities are anticipated as the group works to maintain its access and intelligence-gathering operations.