All posts tagged "cybersecurity"
-

News
/ 2 months agoThe Growing Challenge of Enterprise Identity Management and the Rise of Visibility Platforms
Enterprise identity and access management (IAM) is under unprecedented strain. As organizations expand, their digital identity landscape becomes increasingly complex and...
-
News
/ 2 months agoAnthropic’s Claude Mythos AI Uncovers Thousands of Zero-Day Vulnerabilities in Major Tech Systems
In a significant development for cybersecurity, the artificial intelligence firm Anthropic has launched a new initiative leveraging its advanced AI to...
-


Artificial Intelligence
/ 2 months agoMicrosoft Open-Source Toolkit Aims to Secure Autonomous AI Agents in Real-Time
The rapid deployment of autonomous AI agents capable of independent action has created a significant security challenge for enterprises. Traditional governance...
-


News
/ 2 months agoChaos Malware Variant Expands to Target Cloud Infrastructure, Deploys SOCKS Proxy
A newly identified variant of the Chaos malware is actively targeting misconfigured cloud deployments, according to a recent cybersecurity report. This...
-


News
/ 2 months agoIdentity Management Gaps Pose Growing Enterprise Risk as AI Capabilities Advance
A significant security paradox is challenging Chief Information Security Officers and enterprise leaders. Despite ongoing maturation of identity and access management...
-

News
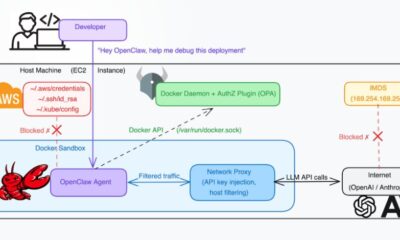
/ 2 months agoCritical Docker Engine Flaw CVE-2026-34040 Enables Authorization Bypass, Host Access
A significant security vulnerability has been identified in Docker Engine, posing a substantial risk to containerized environments. The flaw, cataloged as...
-


News
/ 2 months agoCryptomining Botnet Exploits Over 1,000 Exposed ComfyUI Installations
Security researchers have identified an active and widespread campaign targeting publicly accessible instances of ComfyUI. This popular graphical user interface for...
-


News
/ 2 months agoBeyond the Breach: The Cumulative Financial Drain of Recurring Credential Compromises
In cybersecurity discussions, the dominant narrative is almost invariably one of prevention. This focus is understandable, given the staggering financial figures...
-


Tech News
/ 2 months agoMen Exploit Digital Tools for Intimate Partner Surveillance and Abuse
A disturbing trend has emerged within private online communities where men are reportedly acquiring and deploying digital surveillance tools against women...
-


News
/ 2 months agoNew GPU Security Flaw, GPUBreach, Exploits Memory to Escalate Privileges
A significant new cybersecurity vulnerability has been identified in high performance graphics processing units, or GPUs. Academic researchers have documented a...
















